Actionable & Continuous Vulnerability Management Services
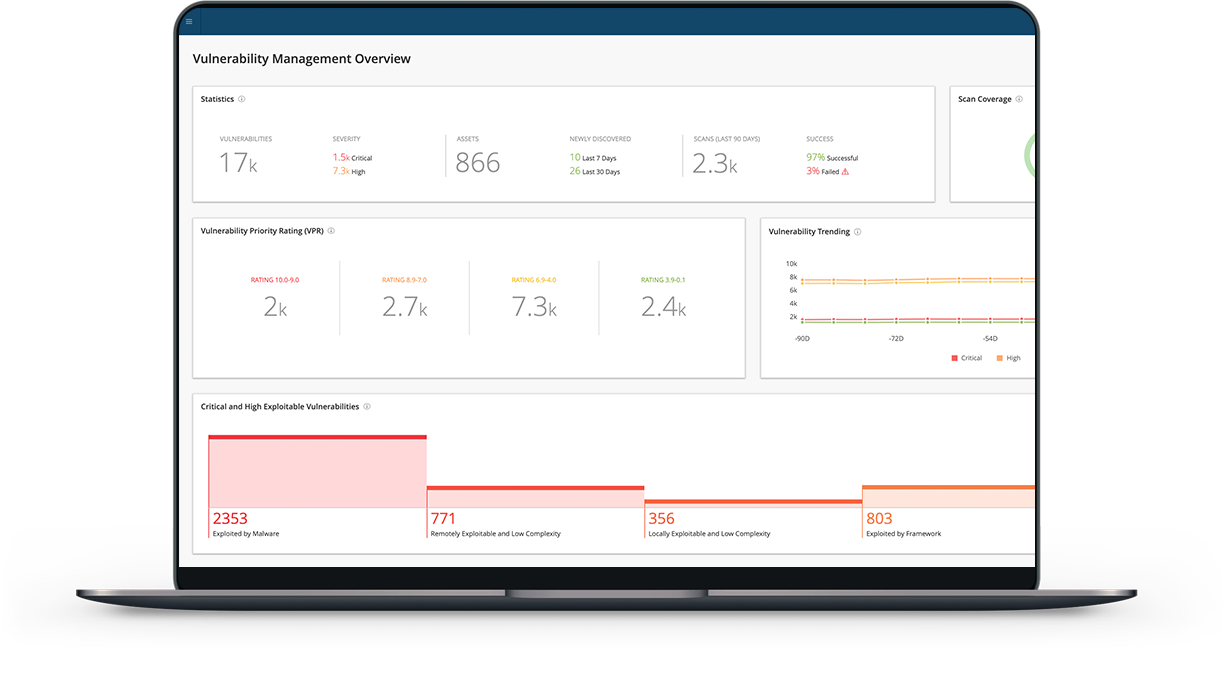
See everything and accurately predict what matters with the most intelligent risk-based managed vulnerability management services system for a wholesome view of your cyber exposure.
Continuous Scans
Vulnerability Prioritization
Actionable Remediation
A Risk-Based View of Your Attack Surface
Devices, tools and users are constantly being added to your network and widening the attack surface. Every new addition adds another possibility for misconfiguration and vulnerabilities. The longer a vulnerability goes undetected, the greater the risk. Sound familiar? Security teams across industries all live this reality every day.
BriteProtect vulnerability management services gives you a risk-based view of your entire attack surface- from IT to cloud to OT and containers. Brite’s team then analyzes results, helps prioritize and guides remediation of vulnerabilities. The end result is increased productivity with the ability to focus efforts where they will have the most impact. Finally, continuous scans ensure constant improvement and confirmation that new risks have not emerged.
We solve your vulnerability management challenges
Unmanageable CVE List?
Living in Vulnerability denial?
Don't know how to remediate vulnerabilities?
Request Vulnerability Management Help Today
Regular Vulnerability Scans
BriteProtect leverages industry-leading, cloud-based Tenable.io for expert vulnerability management services to conduct weekly scans of the environment. Go beyond regulation requirements and gain real insight from vulnerability scans by seeing changes – both positive and negative – in your environment.
Expertly Analyzed for Actionable Risk Assessment Report
The Brite team of vulnerability management analysts review the scans. Knowledge of the customer’s current environment and industry trends are combined to deliver an easy to follow list of vulnerabilities.
Prioritized List of Vulnerabilities
The end result is an easy to follow, prioritized list of vulnerabilities based on its potential business impact. Gone are the days of daunting lists of vulnerabilities with little focus. BriteProtect’s vulnerability management services ensure effort is spent where most effective.
Actionable Remediation Steps
Gain control with comprehensive remediation steps for priority vulnerabilities. Be confident in the security of the environment when remediation is completed. Additionally, see improvements in the security posture with weekly scans.
Patch Management and Remediation Services
Take vulnerability management services to the next level with patching and remediation through BriteStar, the most comprehensive managed IT service. Off-load tactical elements of vulnerability management remediation to the Brite team.

